What is Spoofing and How to Prevent a Spoofing Attack
Spoofing is a cyber attack that occurs when a scammer is disguised as a trusted source to gain access to important data or information. Spoofing can happen through websites, emails, phone calls, texts, IP addresses and servers.
Usually, the main goal of spoofing is to access personal information, steal money, bypass network access controls or spread malware through infected attachments or links. With every form of communication online, scammers will try to use spoofing to try to steal your identity and assets.
Read more to learn about how spoofing happens and how to prevent spoofing attacks.
How does Spoofing Happen?
The term “spoof” dates back over a century and refers to any form of trickery. However, today it’s mostly used when talking about cybercrime. Any time a scammer disguises their identity as another, it’s spoofing.
Spoofing can apply to a number of communication channels and engage different levels of technical know-how. For it to be successful, the spoofing attack has to incorporate a certain level of social engineering. This means that the methods that scammers use are able to effectively trick their victims into giving out their personal information. Scammers use social engineering to play on vulnerable human characteristics, such as greed, fear, and naivety.
An example of this type of social engineering is where the scammer relies on the victim’s feelings of fear in an attempt to gain information or money. The grandchildren scam is when a scammer pretends to be a family member and allegedly states that they’re in trouble and need money as soon as possible. Scammers will often target the elderly in these situations due to the preconceived notion that the elderly are less tech-savvy.
How to Protect Against Spoofing Attacks
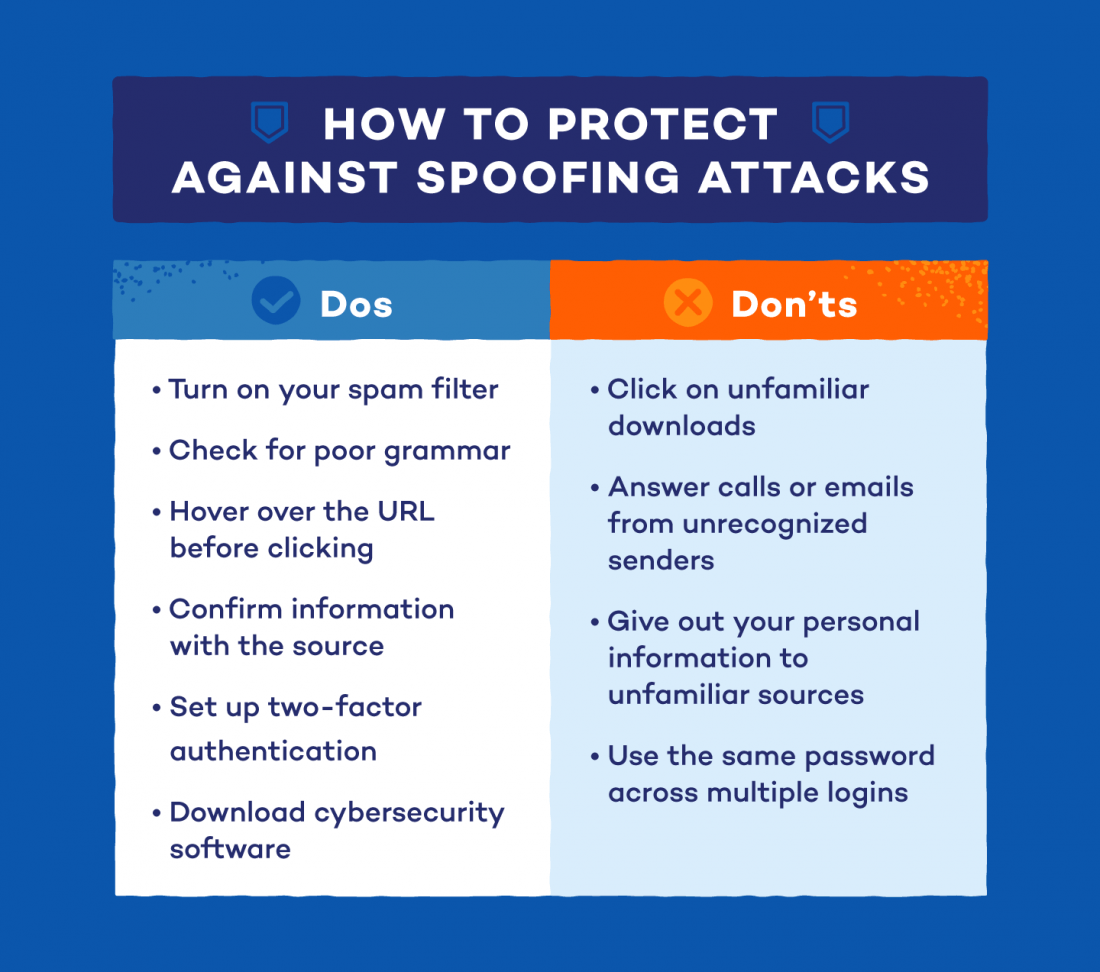
There are many things you can do to protect yourself against spoofing attacks. Stay one step ahead of scammers with these helpful do’s and don’ts:
Do:
- Switch on your spam filter: This will prevent most spoofed emails from coming into your inbox.
- Examine the communication: If the potential spoof attack contains signs of poor grammar or unusual sentence structure, it may be an illegitimate request. Also, be sure to double-check the URL address of a website or the email sender address.
- Confirm the information: If an email or call seems suspicious, send a message or make a call to the sender to confirm that the information you received is legitimate or not.
- Hover before clicking: If a URL looks suspicious, hover your mouse over the link so that you’ll know exactly where the page is going to take you before you click on it.
- Set up two-factor authentication: Setting up two-factor authentication is a great way to add another layer to your passcodes. However, it’s not completely foolproof, so ensure you’re considering other security precautions as well.
- Invest in cybersecurity software: Installing cybersecurity software is the biggest defense when it comes to protecting yourself from scammers online. If you run into trouble, download malware removal or antivirus software to protect your computer from any malicious threats or viruses.
Don’t:
- Don’t click unfamiliar links or downloads: If a link or download file doesn’t look legitimate, refrain from clicking on them. If they’re from an attacker, they’ll usually contain malware or other viruses that can infect your computer.
- Don’t answer emails or calls from unrecognized senders: If the sender is unrecognizable, don’t answer the call or email. This can help prevent any communication with a potential scammer.
- Don’t give out personal information: Avoid giving out your personal and private information, such as a credit card or social security number, unless you’re sure it’s a trusted source.
- Don’t use the same password: Create stronger passwords for your logins that are harder for scammers to guess. Change them frequently in case a scammer gets a hold of one. Also, steer away from using the same password for most of your logins.
If you think you’ve been spoofed, you can file a report with
Action Fraud. You can also contact your local police if you’ve lost money due to spoofing. Be sure to check out our
protection plans to secure your digital life today and protect yourself against spoofing.
Follow Us
Be the first to know
You might also like